Presentation database security audit vault & database firewall
12 likes3,672 views
The document discusses various Oracle database security features, including the Oracle Audit Vault, which consolidates audit data and provides automated activity monitoring and compliance reporting. It emphasizes the importance of detective controls for monitoring privileged user accounts and ensuring compliant access to sensitive data. Additionally, it highlights the Oracle Database Firewall as a protective measure against unauthorized access and the flexible deployment options available for database security management.
1 of 32































Ad
Recommended
Introducing Oracle Audit Vault and Database Firewall
Introducing Oracle Audit Vault and Database FirewallTroy Kitch The document presents an overview of Oracle Audit Vault and Database Firewall, highlighting the vulnerabilities of databases to security breaches and the need for comprehensive security solutions. It outlines Oracle's defense-in-depth strategies, including encryption, activity monitoring, and threat detection, while addressing SQL injection attacks and regulatory compliance across various industries. Through case studies, it demonstrates the effectiveness of these solutions in protecting sensitive data and enhancing database security for organizations.
AV/DF Advanced Security Option
AV/DF Advanced Security OptionDLT Solutions This document discusses database security solutions from Oracle, including Oracle Audit Vault and Database Firewall. It provides an overview of the Oracle Database Security solutions for activity monitoring, database firewalling, auditing and reporting, and encryption. It then focuses on describing the features and benefits of Oracle Audit Vault and Database Firewall, including how they provide database activity auditing and monitoring, extensive reporting, powerful alerting, and strengthened data security.
Ppt dbsec-oow2013-avdf
Ppt dbsec-oow2013-avdfMelody Liu Oracle Audit Vault and Database Firewall provide first line of defense for data security. Audit Vault collects audit data from multiple sources and stores it in a central repository, while Database Firewall monitors database activity in real-time and protects against SQL injections using positive and negative policy models. Both products support extensive reporting, alerting, and flexible deployment across the enterprise.
Oracle Security Presentation
Oracle Security PresentationFrancisco Alvarez This document provides tips and best practices for securing Oracle databases. It begins with an introduction to the speaker, Francisco Munoz Alvarez, who is an Oracle ACE Director. The bulk of the document then lists 27 security tips for Oracle databases, such as granting only necessary privileges to users, encrypting passwords, implementing strong audit policies, and more. It concludes with a brief description of the Oracle ACE program, which recognizes individuals who contribute to Oracle technology communities.
Oracle Audit vault
Oracle Audit vaultuzzal basak Oracle Audit Vault allows monitoring of auditing information from multiple databases in a single centralized location. The key steps to implement Oracle Audit Vault are:
1. Download the Audit Vault software and install it on a server.
2. Register databases as hosts and deploy agents to these databases to capture and send audit records.
3. Configure audit settings in the databases to define what activities to audit.
4. Access the Audit Vault console to view reports, alerts, and retrieve audit records from registered databases.
Technology Overview - Symantec Data Loss Prevention (DLP)
Technology Overview - Symantec Data Loss Prevention (DLP)Iftikhar Ali Iqbal Symantec's Data Loss Prevention (DLP) solution provides comprehensive protection against data leaks by identifying and managing sensitive information across various platforms, including cloud and mobile environments. The solution encompasses features such as monitoring, incident response, and policy enforcement, aimed at safeguarding confidential data from unauthorized access and loss. Key components include endpoint, network, storage, and mobile DLP functionalities, ensuring a robust defense against cyber threats and compliance with governance regulations.
Oracle Database Vault
Oracle Database VaultMarco Alamanni The document discusses Oracle Database Vault, which provides an integrated security framework to control access to databases based on factors like network, users, privileges, roles, and SQL commands. It achieves separation of duties and prevents misuse of powerful privileges. Database Vault enforces compliance requirements and supports database consolidation while requiring no application changes and having minimal performance impact.
Oracle Database Overview
Oracle Database Overviewhonglee71 An Oracle database instance consists of background processes that control one or more databases. A schema is a set of database objects owned by a user that apply to a specific application. Tables store data in rows and columns, and indexes and constraints help maintain data integrity and improve query performance. Database administrators perform tasks like installing and upgrading databases, managing storage, security, backups and high availability.
Oracle Performance Tuning Fundamentals
Oracle Performance Tuning FundamentalsEnkitec The document discusses Oracle performance tuning fundamentals, emphasizing the importance of reducing user wait times, optimizing resource use, and improving system throughput and response time. It covers various aspects of performance tuning such as monitoring tools, wait events, session types, and dynamic performance views, as well as strategies for effective performance analysis. The document highlights the complexity of performance tuning and offers techniques for understanding and managing system performance metrics.
Oracle Enterprise Manager Cloud Control 13c for DBAs
Oracle Enterprise Manager Cloud Control 13c for DBAsGokhan Atil This document provides an overview of Oracle Enterprise Manager Cloud Control 13c for database administrators. It begins with introductions to the presenter and an agenda. It then discusses what Enterprise Manager is, its architecture involving agents, management server, and repository. Some key benefits for DBAs are standardized automation of tasks using a single tool. The document outlines several top features for DBAs, including monitoring, metrics/alerts, incident management, corrective actions, provisioning, patching, ASH analytics, and AWR warehouse. It provides guidance on installing EM13c and post-install tasks. Finally, it covers maintaining EM through tasks like backups, agent management, and keeping everything updated.
User, roles and privileges
User, roles and privilegesYogiji Creations The document discusses managing users, roles, and privileges in Oracle databases. It covers creating, altering, and dropping users, viewing user information, predefined user accounts, different types of privileges including system privileges and object privileges, and user roles. It provides examples and descriptions of commands for working with users, roles, and privileges in Oracle databases.
Isms awareness training
Isms awareness trainingSAROJ BEHERA This document serves as a comprehensive guide on Information Security Management Systems (ISMS) based on ISO/IEC 27001:2005. It emphasizes the importance of properly protecting information as a vital organizational asset and outlines key components such as risk management, security strategies involving people, processes, and technology, and the necessity of compliance with international standards. Additionally, it discusses the roles of various stakeholders in information security, classifications of information assets, and the overarching aim of maintaining confidentiality, integrity, and availability of information.
ISO 27001 (v2013) Checklist
ISO 27001 (v2013) ChecklistIvan Piskunov The document is a comprehensive compliance assessment focused on information security policies and procedures. It outlines various standards and findings concerning management direction, organizational roles, human resources security, asset management, access control, and incident management. The assessment covers requirements for documentation, processes, and compliance with legal and regulatory standards across multiple aspects of information security.
Enterprise Security Architecture
Enterprise Security ArchitecturePriyanka Aash The document discusses enterprise security architecture, highlighting the importance of comprehensive methods for defining security across systems. It explores the Zachman framework for organizing architectural artifacts and introduces the SABSA model as a business-driven approach to security architecture. SABSA emphasizes alignment with business goals, risk management, and provides a detailed lifecycle for security architecture development.
Oracle Transparent Data Encryption (TDE) 12c
Oracle Transparent Data Encryption (TDE) 12cNabeel Yoosuf Oracle Transparent Data Encryption (TDE) 12c is an advanced security feature that encrypts data-at-rest, protecting it from unauthorized access, particularly for sensitive tables and columns. The setup involves creating an Oracle wallet to store the TDE master key and following specific steps to encrypt targeted data. While TDE provides options for both column and tablespace encryption, it has limitations including overhead costs and restrictions on index types.
Standard Edition High Availability (SEHA) - The Why, What & How
Standard Edition High Availability (SEHA) - The Why, What & HowMarkus Michalewicz The document discusses Oracle's Standard Edition High Availability (SEHA), a solution designed for Single-Instance Oracle databases that provides integrated cluster-based failover using Oracle Clusterware. It outlines the features, requirements, and setup process for SEHA, emphasizing its speed and capability to support high availability and disaster recovery for small to mid-sized enterprises. Additionally, it explains the differences between SEHA and other Oracle database editions, including licensing considerations and alternative paths to upgrade.
Data Loss Prevention (DLP) - Fundamental Concept - Eryk
Data Loss Prevention (DLP) - Fundamental Concept - ErykEryk Budi Pratama This document discusses data loss prevention (DLP) concepts and implementations. It begins with an overview of data governance and the data lifecycle. It then defines DLP, explaining how DLP solutions protect data in motion, at rest, and in use. Sample DLP deployments are shown, outlining key activities and considerations for implementation such as governance, infrastructure, and a phased approach. Finally, examples of DLP use cases are provided for data in motion like email and data in use on workstations.
Oracle DBA
Oracle DBAshivankuniversity The document is a comprehensive guide to database administration, specifically focusing on Oracle 10g and 11g, covering tasks, tools, and user account management. It details the roles and responsibilities of a Database Administrator (DBA), performance management, security, and usage of Oracle Enterprise Manager for database operations. Furthermore, it explains data storage structures, including tablespaces and data files, and highlights additional DBA activities such as backups, recovery, and auditing.
Migration to Oracle Multitenant
Migration to Oracle MultitenantJitendra Singh This document discusses upgrading to Oracle Database 19c and migrating to Oracle Multitenant. It provides an overview of key features such as being able to have 3 user-created PDBs without a Multitenant license in 19c. It also demonstrates how to use AutoUpgrade to perform an upgrade and migration to Multitenant with a single command. The document highlights various Multitenant concepts such as resource sharing, connecting to containers, and cloning PDBs.
Oracle EBS R12.2 - Deployment and System Administration
Oracle EBS R12.2 - Deployment and System AdministrationMozammel Hoque The document outlines a comprehensive training program on Oracle E-Business Suite R12.2.x, focusing on deployment and system administration. Presented by MD Mozammel Hoque, it aims to enhance operational efficiency and minimize maintenance downtimes while covering topics like technology architecture, performance tuning, and IT service continuity management. The training also includes practical lab sessions, case studies, and highlights the significant benefits of the Oracle E-Business Suite technology for enterprises.
Oracle Database Security
Oracle Database SecurityTroy Kitch The document discusses security issues with databases and Oracle's database security solutions. It notes that 97% of breaches were avoidable with basic controls, 98% of records were stolen from databases, and 84% of records were breached using stolen credentials. Oracle provides database security solutions like encryption, activity monitoring, auditing, and privileged user controls to help prevent breaches through a defense-in-depth approach.
introduction to Azure Sentinel
introduction to Azure SentinelRobert Crane Azure Sentinel is Microsoft's cloud-native security information and event management (SIEM) and security orchestration, automation and response (SOAR) solution. It provides intelligent security analytics and threat detection across on-premises, cloud, and hybrid environments. Azure Sentinel collects data from various sources using connectors and agents, then analyzes the data using machine learning to detect threats and automate responses. It integrates with other Microsoft security solutions and allows threat hunting and visualization of security incidents.
What’s New in Oracle Database 19c - Part 1
What’s New in Oracle Database 19c - Part 1Satishbabu Gunukula Oracle Database 19c is the final release of the Oracle Database 12c family, featuring enhancements in installation, configuration, and various functionalities including application development, security, and performance improvements. New significant features include automated utilities, advanced JSON support, and enhanced capabilities for big data and data warehousing. This version also provides extensive support for high availability and advanced diagnostical tools, solidifying its position as a robust solution for modern database management.
Oracle Enterprise Manager Cloud Control 13c for DBAs
Oracle Enterprise Manager Cloud Control 13c for DBAsGokhan Atil This document provides an overview and introduction to Oracle Enterprise Manager Cloud Control 13c (EM13c) for database administrators (DBAs). It discusses the key features and benefits of EM13c for monitoring, performance tuning, and provisioning databases. The document outlines the architecture and components of EM13c and why it is useful for centralized management. It also provides tips for DBAs on using features like monitoring, incident management, ASH analytics, provisioning, patching, and best practices for installation, configuration, and maintenance of an EM13c environment.
Data Guard Architecture & Setup
Data Guard Architecture & SetupSatishbabu Gunukula This document provides an overview and summary of Oracle Data Guard. It discusses the key benefits of Data Guard including disaster recovery, data protection, and high availability. It describes the different types of Data Guard configurations including physical and logical standbys. The document outlines the basic architecture and processes involved in implementing Data Guard including redo transport, apply services, and role transitions. It also summarizes some of the features and protection modes available in different Oracle database versions.
RMAN in 12c: The Next Generation (PPT)
RMAN in 12c: The Next Generation (PPT)Gustavo Rene Antunez The document presents an overview of RMAN in Oracle 12c, detailing its capabilities for backup and recovery within multitenant architecture, including pluggable databases. It highlights features like sysbackup privilege, SQL interface improvements, and active database duplication, while emphasizing the importance of properly configuring RMAN backups. Additionally, the document outlines specific commands and considerations for managing RMAN settings and showcases examples of backup operations.
How can the ISO 27701 help to design, implement, operate and improve a privac...
How can the ISO 27701 help to design, implement, operate and improve a privac...Hernan Huwyler, MBA CPA The document discusses how ISO 27701 can assist organizations in establishing and enhancing a privacy information management system, covering areas like application controls, data protection compliance, risk assessment, policy management, and user management. It outlines specific controls for managing personal data, including technical, legal, and security measures, as well as the importance of training and awareness for employees. Additionally, it stresses the need for ongoing compliance and the role of a privacy officer in adhering to privacy laws and best practices.
Oracle dba training
Oracle dba training P S Rani This document provides an overview of Oracle DBA training topics including relational database management systems (RDBMS), RDBMS and SQL, DBA tasks, Oracle database architecture, Oracle instance architecture, background processes, system global area (SGA), shared pool, library cache, and data dictionary cache. Key points covered include how RDBMS stores and accesses data through tables, the roles of consistency and concurrency in RDBMS, common DBA responsibilities like installation, backup/recovery, monitoring and performance tuning, and important components that make up the Oracle database architecture like instances, processes, memory structures, and caches.
Security Inside Out: Latest Innovations in Oracle Database 12c
Security Inside Out: Latest Innovations in Oracle Database 12cTroy Kitch The document outlines Oracle's product direction and security solutions, highlighting the importance of database security amid increasing data breaches and cyber threats. It emphasizes key features of Oracle Database 12c, including real-time activity monitoring, encryption, redaction, and privileged user controls. The content serves as an informational resource, not a binding commitment to deliver specific functionality or features.
Oracle 11g security - 2014
Oracle 11g security - 2014Connor McDonald The document discusses Oracle's database security solutions. It notes that data security is a top priority for enterprises and that more data and breaches are occurring than ever before. It then summarizes Oracle's solutions like Database Firewall, Configuration Management, Total Recall, Audit Vault, Database Vault, and Data Masking which provide capabilities like monitoring, access control, auditing, encryption, and identity management to help secure database environments with a defense-in-depth approach.
More Related Content
What's hot (20)
Oracle Performance Tuning Fundamentals
Oracle Performance Tuning FundamentalsEnkitec The document discusses Oracle performance tuning fundamentals, emphasizing the importance of reducing user wait times, optimizing resource use, and improving system throughput and response time. It covers various aspects of performance tuning such as monitoring tools, wait events, session types, and dynamic performance views, as well as strategies for effective performance analysis. The document highlights the complexity of performance tuning and offers techniques for understanding and managing system performance metrics.
Oracle Enterprise Manager Cloud Control 13c for DBAs
Oracle Enterprise Manager Cloud Control 13c for DBAsGokhan Atil This document provides an overview of Oracle Enterprise Manager Cloud Control 13c for database administrators. It begins with introductions to the presenter and an agenda. It then discusses what Enterprise Manager is, its architecture involving agents, management server, and repository. Some key benefits for DBAs are standardized automation of tasks using a single tool. The document outlines several top features for DBAs, including monitoring, metrics/alerts, incident management, corrective actions, provisioning, patching, ASH analytics, and AWR warehouse. It provides guidance on installing EM13c and post-install tasks. Finally, it covers maintaining EM through tasks like backups, agent management, and keeping everything updated.
User, roles and privileges
User, roles and privilegesYogiji Creations The document discusses managing users, roles, and privileges in Oracle databases. It covers creating, altering, and dropping users, viewing user information, predefined user accounts, different types of privileges including system privileges and object privileges, and user roles. It provides examples and descriptions of commands for working with users, roles, and privileges in Oracle databases.
Isms awareness training
Isms awareness trainingSAROJ BEHERA This document serves as a comprehensive guide on Information Security Management Systems (ISMS) based on ISO/IEC 27001:2005. It emphasizes the importance of properly protecting information as a vital organizational asset and outlines key components such as risk management, security strategies involving people, processes, and technology, and the necessity of compliance with international standards. Additionally, it discusses the roles of various stakeholders in information security, classifications of information assets, and the overarching aim of maintaining confidentiality, integrity, and availability of information.
ISO 27001 (v2013) Checklist
ISO 27001 (v2013) ChecklistIvan Piskunov The document is a comprehensive compliance assessment focused on information security policies and procedures. It outlines various standards and findings concerning management direction, organizational roles, human resources security, asset management, access control, and incident management. The assessment covers requirements for documentation, processes, and compliance with legal and regulatory standards across multiple aspects of information security.
Enterprise Security Architecture
Enterprise Security ArchitecturePriyanka Aash The document discusses enterprise security architecture, highlighting the importance of comprehensive methods for defining security across systems. It explores the Zachman framework for organizing architectural artifacts and introduces the SABSA model as a business-driven approach to security architecture. SABSA emphasizes alignment with business goals, risk management, and provides a detailed lifecycle for security architecture development.
Oracle Transparent Data Encryption (TDE) 12c
Oracle Transparent Data Encryption (TDE) 12cNabeel Yoosuf Oracle Transparent Data Encryption (TDE) 12c is an advanced security feature that encrypts data-at-rest, protecting it from unauthorized access, particularly for sensitive tables and columns. The setup involves creating an Oracle wallet to store the TDE master key and following specific steps to encrypt targeted data. While TDE provides options for both column and tablespace encryption, it has limitations including overhead costs and restrictions on index types.
Standard Edition High Availability (SEHA) - The Why, What & How
Standard Edition High Availability (SEHA) - The Why, What & HowMarkus Michalewicz The document discusses Oracle's Standard Edition High Availability (SEHA), a solution designed for Single-Instance Oracle databases that provides integrated cluster-based failover using Oracle Clusterware. It outlines the features, requirements, and setup process for SEHA, emphasizing its speed and capability to support high availability and disaster recovery for small to mid-sized enterprises. Additionally, it explains the differences between SEHA and other Oracle database editions, including licensing considerations and alternative paths to upgrade.
Data Loss Prevention (DLP) - Fundamental Concept - Eryk
Data Loss Prevention (DLP) - Fundamental Concept - ErykEryk Budi Pratama This document discusses data loss prevention (DLP) concepts and implementations. It begins with an overview of data governance and the data lifecycle. It then defines DLP, explaining how DLP solutions protect data in motion, at rest, and in use. Sample DLP deployments are shown, outlining key activities and considerations for implementation such as governance, infrastructure, and a phased approach. Finally, examples of DLP use cases are provided for data in motion like email and data in use on workstations.
Oracle DBA
Oracle DBAshivankuniversity The document is a comprehensive guide to database administration, specifically focusing on Oracle 10g and 11g, covering tasks, tools, and user account management. It details the roles and responsibilities of a Database Administrator (DBA), performance management, security, and usage of Oracle Enterprise Manager for database operations. Furthermore, it explains data storage structures, including tablespaces and data files, and highlights additional DBA activities such as backups, recovery, and auditing.
Migration to Oracle Multitenant
Migration to Oracle MultitenantJitendra Singh This document discusses upgrading to Oracle Database 19c and migrating to Oracle Multitenant. It provides an overview of key features such as being able to have 3 user-created PDBs without a Multitenant license in 19c. It also demonstrates how to use AutoUpgrade to perform an upgrade and migration to Multitenant with a single command. The document highlights various Multitenant concepts such as resource sharing, connecting to containers, and cloning PDBs.
Oracle EBS R12.2 - Deployment and System Administration
Oracle EBS R12.2 - Deployment and System AdministrationMozammel Hoque The document outlines a comprehensive training program on Oracle E-Business Suite R12.2.x, focusing on deployment and system administration. Presented by MD Mozammel Hoque, it aims to enhance operational efficiency and minimize maintenance downtimes while covering topics like technology architecture, performance tuning, and IT service continuity management. The training also includes practical lab sessions, case studies, and highlights the significant benefits of the Oracle E-Business Suite technology for enterprises.
Oracle Database Security
Oracle Database SecurityTroy Kitch The document discusses security issues with databases and Oracle's database security solutions. It notes that 97% of breaches were avoidable with basic controls, 98% of records were stolen from databases, and 84% of records were breached using stolen credentials. Oracle provides database security solutions like encryption, activity monitoring, auditing, and privileged user controls to help prevent breaches through a defense-in-depth approach.
introduction to Azure Sentinel
introduction to Azure SentinelRobert Crane Azure Sentinel is Microsoft's cloud-native security information and event management (SIEM) and security orchestration, automation and response (SOAR) solution. It provides intelligent security analytics and threat detection across on-premises, cloud, and hybrid environments. Azure Sentinel collects data from various sources using connectors and agents, then analyzes the data using machine learning to detect threats and automate responses. It integrates with other Microsoft security solutions and allows threat hunting and visualization of security incidents.
What’s New in Oracle Database 19c - Part 1
What’s New in Oracle Database 19c - Part 1Satishbabu Gunukula Oracle Database 19c is the final release of the Oracle Database 12c family, featuring enhancements in installation, configuration, and various functionalities including application development, security, and performance improvements. New significant features include automated utilities, advanced JSON support, and enhanced capabilities for big data and data warehousing. This version also provides extensive support for high availability and advanced diagnostical tools, solidifying its position as a robust solution for modern database management.
Oracle Enterprise Manager Cloud Control 13c for DBAs
Oracle Enterprise Manager Cloud Control 13c for DBAsGokhan Atil This document provides an overview and introduction to Oracle Enterprise Manager Cloud Control 13c (EM13c) for database administrators (DBAs). It discusses the key features and benefits of EM13c for monitoring, performance tuning, and provisioning databases. The document outlines the architecture and components of EM13c and why it is useful for centralized management. It also provides tips for DBAs on using features like monitoring, incident management, ASH analytics, provisioning, patching, and best practices for installation, configuration, and maintenance of an EM13c environment.
Data Guard Architecture & Setup
Data Guard Architecture & SetupSatishbabu Gunukula This document provides an overview and summary of Oracle Data Guard. It discusses the key benefits of Data Guard including disaster recovery, data protection, and high availability. It describes the different types of Data Guard configurations including physical and logical standbys. The document outlines the basic architecture and processes involved in implementing Data Guard including redo transport, apply services, and role transitions. It also summarizes some of the features and protection modes available in different Oracle database versions.
RMAN in 12c: The Next Generation (PPT)
RMAN in 12c: The Next Generation (PPT)Gustavo Rene Antunez The document presents an overview of RMAN in Oracle 12c, detailing its capabilities for backup and recovery within multitenant architecture, including pluggable databases. It highlights features like sysbackup privilege, SQL interface improvements, and active database duplication, while emphasizing the importance of properly configuring RMAN backups. Additionally, the document outlines specific commands and considerations for managing RMAN settings and showcases examples of backup operations.
How can the ISO 27701 help to design, implement, operate and improve a privac...
How can the ISO 27701 help to design, implement, operate and improve a privac...Hernan Huwyler, MBA CPA The document discusses how ISO 27701 can assist organizations in establishing and enhancing a privacy information management system, covering areas like application controls, data protection compliance, risk assessment, policy management, and user management. It outlines specific controls for managing personal data, including technical, legal, and security measures, as well as the importance of training and awareness for employees. Additionally, it stresses the need for ongoing compliance and the role of a privacy officer in adhering to privacy laws and best practices.
Oracle dba training
Oracle dba training P S Rani This document provides an overview of Oracle DBA training topics including relational database management systems (RDBMS), RDBMS and SQL, DBA tasks, Oracle database architecture, Oracle instance architecture, background processes, system global area (SGA), shared pool, library cache, and data dictionary cache. Key points covered include how RDBMS stores and accesses data through tables, the roles of consistency and concurrency in RDBMS, common DBA responsibilities like installation, backup/recovery, monitoring and performance tuning, and important components that make up the Oracle database architecture like instances, processes, memory structures, and caches.
How can the ISO 27701 help to design, implement, operate and improve a privac...
How can the ISO 27701 help to design, implement, operate and improve a privac...Hernan Huwyler, MBA CPA
Similar to Presentation database security audit vault & database firewall (20)
Security Inside Out: Latest Innovations in Oracle Database 12c
Security Inside Out: Latest Innovations in Oracle Database 12cTroy Kitch The document outlines Oracle's product direction and security solutions, highlighting the importance of database security amid increasing data breaches and cyber threats. It emphasizes key features of Oracle Database 12c, including real-time activity monitoring, encryption, redaction, and privileged user controls. The content serves as an informational resource, not a binding commitment to deliver specific functionality or features.
Oracle 11g security - 2014
Oracle 11g security - 2014Connor McDonald The document discusses Oracle's database security solutions. It notes that data security is a top priority for enterprises and that more data and breaches are occurring than ever before. It then summarizes Oracle's solutions like Database Firewall, Configuration Management, Total Recall, Audit Vault, Database Vault, and Data Masking which provide capabilities like monitoring, access control, auditing, encryption, and identity management to help secure database environments with a defense-in-depth approach.
Oracle Database 23c Security New Features.pptx
Oracle Database 23c Security New Features.pptxSatishbabu Gunukula Oracle Database 23c introduces advanced security features including SQL firewall for real-time protection against SQL injection and unauthorized access, along with refined encryption methods using TLS 1.3. Enhancements in authentication, such as Azure AD integration and longer password support, improve security while ensuring compliance for audit actions on specific columns. The upgrade offers robust encryption, auditing capabilities, and centralized management for better overall database security.
Database security best_practices
Database security best_practicesTarik Essawi This presentation provided techniques for securing an Oracle database, including: securing Oracle binaries and dump files; restricting and monitoring the listener; limiting privileges and authentication; implementing comprehensive auditing; and protecting data outside of production. The key areas discussed were securing the database binaries and directories, protecting the listener as a single point of failure, following the principle of least privilege, auditing for privilege escalation and changes to the audit trail, and securing backups and development data. The overall message was that firewalls alone are not enough and a layered security approach is needed to properly secure an Oracle database.
Database Private Security Jurisprudence: A Case Study using Oracle
Database Private Security Jurisprudence: A Case Study using OracleIJDMS The document discusses the importance of securing Oracle databases against various types of attacks, including insider and outsider threats, by offering practical guidelines for hardening database security. It highlights potential vulnerabilities, authentication mechanisms, and access control models, as well as specific strategies to protect against unauthorized access and data breaches. Furthermore, the paper provides SQL syntax examples to illustrate these security measures and emphasizes the critical role of regular updates and proper privilege assignments to maintain database integrity.
DATABASE PRIVATE SECURITY JURISPRUDENCE: A CASE STUDY USING ORACLE
DATABASE PRIVATE SECURITY JURISPRUDENCE: A CASE STUDY USING ORACLEIJDMS This paper discusses database security, specifically focusing on hardening Oracle databases against various types of attacks, including those from insiders and outsiders. It provides practical guidelines and examples for protecting database access and privileges, utilizing features such as encryption and auditing. The study emphasizes the importance of user responsibility, access control mechanisms, and constant updates to secure databases effectively.
Oracle Database 11g Security and Compliance Solutions - By Tom Kyte
Oracle Database 11g Security and Compliance Solutions - By Tom KyteEdgar Alejandro Villegas The document discusses database security best practices and outlines the importance of protecting sensitive information stored in databases. It highlights challenges, industry statistics regarding data breaches, and provides recommendations for implementing robust security measures, such as access control and data encryption. Additionally, it emphasizes the need for organizations to develop a comprehensive database security plan to mitigate risks and comply with regulations.
Vault_KT.pptx
Vault_KT.pptxSDPL Technologies This document provides an agenda and overview of Oracle Database Vault. It discusses Database Vault features like realms and rule sets that provide controls for privileged accounts and enforce separation of duties. It provides recommendations for prerequisites like an existing security concept and hardening. It also discusses alternatives to Database Vault like activity monitoring tools and the importance of accompanying measures like Transparent Data Encryption.
DOAG Oracle Database Vault
DOAG Oracle Database VaultStefan Oehrli The document outlines the features and functionalities of Oracle Database Vault, which is designed to protect sensitive data from unauthorized access and misuse. It highlights the importance of implementing basic security measures and advanced controls for database administration while also addressing the need for segregation of duties among users. Additional considerations include regular security audits, integration with Oracle's advanced security measures, and evaluating the necessity of such safeguards based on data protection requirements.
Securing data in Oracle Database 12c - 2015
Securing data in Oracle Database 12c - 2015Connor McDonald The document discusses security features in Oracle Database 12c including Transparent Data Encryption (TDE), Privilege Analysis, Database Vault, Database Firewall, Data Redaction, Data Masking, and Audit Vault. It provides an overview of each technology and how they can be used to secure data at rest and in motion, monitor and control privileged access, and audit database activity. The document also outlines an agenda to cover these security controls in more depth.
Varhol oracle database_firewall_oct2011
Varhol oracle database_firewall_oct2011Peter Varhol The document discusses SQL injection attacks and methods for preventing them. It describes SQL injection as malicious SQL code being passed into an application's user input fields. This can result in data corruption, theft, or systems being compromised. The document outlines best practices for preventing SQL injections, such as input validation and output encoding. It then demonstrates how the Oracle Database Firewall provides defenses against SQL injections through features like SQL monitoring, blocking, and auditing.
Less10 security mb3
Less10 security mb3Imran Ali This document discusses implementing security for Oracle databases. It covers DBA responsibilities like applying least privilege and enabling auditing. It describes different types of auditing like standard, value-based, and fine-grained auditing. It also discusses separating responsibilities, maintaining audit trails, and applying security updates. The objectives are to describe DBA security roles, enable auditing, specify audit options, review audits, and maintain audit trails.
5. 2010 11-03 bucharest oracle-tech_day_security
5. 2010 11-03 bucharest oracle-tech_day_securityDoina Draganescu This document outlines Oracle's product direction for data security at the source in public and private sectors. It discusses business drivers for security such as governance, risk management and compliance needs as well as security threats. It then describes Oracle's database security solutions like Transparent Data Encryption, Database Vault, and Audit Vault that secure data at rest, in motion and for testing. Case studies show how customers in various industries like banking, telecom, and public sectors have implemented Oracle's database security to protect sensitive data and comply with regulations. The document concludes that Oracle's database security solutions provide a preventive and detective approach to protect data at the source.
Autonomous Database Security Features
Autonomous Database Security FeaturesSinanPetrusToma This document discusses security features of Oracle Autonomous Database including:
- Encryption of data at rest and in backups using transparent data encryption
- Network access control using access control lists and private endpoints
- System and data protection with features like Database Vault and command restrictions
- Discovery and masking of sensitive data using tools like Data Redaction and Data Safe
- Auditing of database activity, APIs, and network traffic for monitoring and compliance
Oracle database 12c security and compliance
Oracle database 12c security and complianceFITSFSd This document discusses Oracle Database 12c security features. It describes how Oracle Database 12c prevents database bypass, protects against operating system-level data access through transparent data encryption, and manages encryption keys with Oracle Key Vault. The document also covers reducing sensitive data exposure in applications, limiting exposure when sharing data, preventing application bypass, and protecting against privileged user bypass.
how to protect your sensitive data using oracle database vault
how to protect your sensitive data using oracle database vaultAnar Godjaev - Oracle Database Vault provides powerful security controls to help protect sensitive application data from unauthorized access and comply with privacy regulations. It controls privileged account access and sensitive operations inside the database using multi-factor authorization.
- Database Vault realms prevent privileged accounts from accessing application schemas, sensitive tables, and stored procedures. It also controls database configuration changes and prevents unauthorized changes to database entitlements.
- Database Vault is configured easily and runs transparently with minimal performance impact. It implements duty separation, restricting even DBA users' access and controling database operations. Once enabled, it provides strong protection of applications and data.
MySQL Security
MySQL SecurityMario Beck The document discusses MySQL security challenges, highlighting that 43% of companies faced data breaches in the past year and emphasizing the increase in vulnerabilities. It outlines various responsibilities for database administrators, strategies for regulatory compliance, and features such as authentication, encryption, and firewall protections to mitigate risks. Additionally, it provides insights into advanced security measures like auditing, password policies, and real-time protection against SQL injection attacks.
ppt-security-dbsat-222-overview-nodemo.pdf
ppt-security-dbsat-222-overview-nodemo.pdfcamyla81 DBSAT is a security assessment tool from Oracle that allows users to assess the security of their Oracle databases. It provides three main functions: it collects metadata on users, roles, privileges and security configuration; it generates a summary report of findings and recommendations; and it discovers sensitive data in the database. The tool aims to help users understand their database security posture, privileged users and roles, and sensitive data stored in the database.
DB2 LUW Auditing
DB2 LUW AuditingDB2Locksmith DB2 LUW Security introduces new auditing features in DB2 9.5 that make auditing more flexible and granular. Key points include:
- Database auditing now has separate instance and database levels for more flexibility and separation of duties.
- New auditing categories like EXECUTE allow auditing just SQL statements instead of entire operation contexts.
- Audit policies are used at the database level instead of the old db2audit commands. Policies are created and assigned to objects by SECADMs.
- Instance level auditing is still done with db2audit commands by SYSADMs, while database level uses stored procedures delegated by SECADMs.
- The new
Database & Technology 1 _ Barbara Rabinowicz _ Database Security Methoda and ...
Database & Technology 1 _ Barbara Rabinowicz _ Database Security Methoda and ...InSync2011 Barbara Rabinowicz provides an overview of database security methods and techniques. She discusses why database security is important given past hacking incidents. Some key recommendations for hardening an Oracle environment include: securing the physical server location; limiting user privileges and roles; restricting access to sensitive views and tables; and revoking unneeded privileges from publicly executable packages. The document outlines numerous steps to help enhance database security.
Ad
More from xKinAnx (20)
Engage for success ibm spectrum accelerate 2
Engage for success ibm spectrum accelerate 2xKinAnx IBM Spectrum Accelerate is software that extends the capabilities of IBM's XIV storage system, such as consistent performance tuning-free, to new delivery models. It provides enterprise storage capabilities deployed in minutes instead of months. Spectrum Accelerate runs the proven XIV software on commodity x86 servers and storage, providing similar features and functions to an XIV system. It offers benefits like business agility, flexibility, simplified acquisition and deployment, and lower administration and training costs.
Accelerate with ibm storage ibm spectrum virtualize hyper swap deep dive
Accelerate with ibm storage ibm spectrum virtualize hyper swap deep divexKinAnx The document provides an overview of IBM Spectrum Virtualize HyperSwap functionality. HyperSwap allows host I/O to continue accessing volumes across two sites without interruption if one site fails. It uses synchronous remote copy between two I/O groups to make volumes accessible across both groups. The document outlines the steps to configure a HyperSwap configuration, including naming sites, assigning nodes and hosts to sites, and defining the topology.
Software defined storage provisioning using ibm smart cloud
Software defined storage provisioning using ibm smart cloudxKinAnx This document provides an overview of software-defined storage provisioning using IBM SmartCloud Virtual Storage Center (VSC). It discusses the typical challenges with manual storage provisioning, and how VSC addresses those challenges through automation. VSC's storage provisioning involves three phases - setup, planning, and execution. The setup phase involves adding storage devices, servers, and defining service classes. In the planning phase, VSC creates a provisioning plan based on the request. In the execution phase, the plan is run to automatically complete all configuration steps. The document highlights how VSC optimizes placement and streamlines the provisioning process.
Ibm spectrum virtualize 101
Ibm spectrum virtualize 101 xKinAnx This document discusses IBM Spectrum Virtualize 101 and IBM Spectrum Storage solutions. It provides an overview of software defined storage and IBM Spectrum Virtualize, describing how it achieves storage virtualization and mobility. It also provides details on the new IBM Spectrum Virtualize DH8 hardware platform, including its performance improvements over previous platforms and support for compression acceleration.
Accelerate with ibm storage ibm spectrum virtualize hyper swap deep dive dee...
Accelerate with ibm storage ibm spectrum virtualize hyper swap deep dive dee...xKinAnx HyperSwap provides high availability by allowing volumes to be accessible across two IBM Spectrum Virtualize systems in a clustered configuration. It uses synchronous remote copy to replicate primary and secondary volumes between the two systems, making the volumes appear as a single object to hosts. This allows host I/O to continue if an entire system fails without any data loss. The configuration requires a quorum disk in a third site for the cluster to maintain coordination and survive failures across the two main sites.
04 empalis -ibm_spectrum_protect_-_strategy_and_directions
04 empalis -ibm_spectrum_protect_-_strategy_and_directionsxKinAnx IBM Spectrum Protect (formerly IBM Tivoli Storage Manager) provides data protection and recovery for hybrid cloud environments. This document summarizes a presentation on IBM's strategic direction for Spectrum Protect, including plans to enhance the product to better support hybrid cloud, virtual environments, large-scale deduplication, simplified management, and protection for key workloads. The presentation outlines roadmap features for 2015 and potential future enhancements.
Ibm spectrum scale fundamentals workshop for americas part 1 components archi...
Ibm spectrum scale fundamentals workshop for americas part 1 components archi...xKinAnx The document provides instructions for installing and configuring Spectrum Scale 4.1. Key steps include: installing Spectrum Scale software on nodes; creating a cluster using mmcrcluster and designating primary/secondary servers; verifying the cluster status with mmlscluster; creating Network Shared Disks (NSDs); and creating a file system. The document also covers licensing, system requirements, and IBM and client responsibilities for installation and maintenance.
Ibm spectrum scale fundamentals workshop for americas part 2 IBM Spectrum Sca...
Ibm spectrum scale fundamentals workshop for americas part 2 IBM Spectrum Sca...xKinAnx This document discusses quorum nodes in Spectrum Scale clusters and recovery from failures. It describes how quorum nodes determine the active cluster and prevent partitioning. The document outlines best practices for quorum nodes and provides steps to recover from loss of a quorum node majority or failure of the primary and secondary configuration servers.
Ibm spectrum scale fundamentals workshop for americas part 3 Information Life...
Ibm spectrum scale fundamentals workshop for americas part 3 Information Life...xKinAnx IBM Spectrum Scale can help achieve ILM efficiencies through policy-driven, automated tiered storage management. The ILM toolkit manages file sets and storage pools and automates data management. Storage pools group similar disks and classify storage within a file system. File placement and management policies determine file placement and movement based on rules.
Ibm spectrum scale fundamentals workshop for americas part 4 Replication, Str...
Ibm spectrum scale fundamentals workshop for americas part 4 Replication, Str...xKinAnx The document provides an overview of IBM Spectrum Scale Active File Management (AFM). AFM allows data to be accessed globally across multiple clusters as if it were local by automatically managing asynchronous replication. It describes the various AFM modes including read-only caching, single-writer, and independent writer. It also covers topics like pre-fetching data, cache eviction, cache states, expiration of stale data, and the types of data transferred between home and cache sites.
Ibm spectrum scale fundamentals workshop for americas part 4 spectrum scale_r...
Ibm spectrum scale fundamentals workshop for americas part 4 spectrum scale_r...xKinAnx This document provides information about replication and stretch clusters in IBM Spectrum Scale. It defines replication as synchronously copying file system data across failure groups for redundancy. While replication improves availability, it reduces performance and increases storage usage. Stretch clusters combine two or more clusters to create a single large cluster, typically using replication between sites. Replication policies and failure group configuration are important to ensure effective data duplication.
Ibm spectrum scale fundamentals workshop for americas part 5 spectrum scale_c...
Ibm spectrum scale fundamentals workshop for americas part 5 spectrum scale_c...xKinAnx This document provides information about clustered NFS (cNFS) in IBM Spectrum Scale. cNFS allows multiple Spectrum Scale servers to share a common namespace via NFS, providing high availability, performance, scalability and a single namespace as storage capacity increases. The document discusses components of cNFS including load balancing, monitoring, and failover. It also provides instructions for prerequisites, setup, administration and tuning of a cNFS configuration.
Ibm spectrum scale fundamentals workshop for americas part 6 spectrumscale el...
Ibm spectrum scale fundamentals workshop for americas part 6 spectrumscale el...xKinAnx This document provides an overview of managing Spectrum Scale opportunity discovery and working with external resources to be successful. It discusses how to build presentations and configurations to address technical and philosophical solution requirements. The document introduces IBM Spectrum Scale as providing low latency global data access, linear scalability, and enterprise storage services on standard hardware for on-premise or cloud deployments. It also discusses Spectrum Scale and Elastic Storage Server, noting the latter is a hardware building block with GPFS 4.1 installed. The document provides tips for discovering opportunities through RFPs, RFIs, events, workshops, and engaging clients to understand their needs in order to build compelling proposal information.
Ibm spectrum scale fundamentals workshop for americas part 7 spectrumscale el...
Ibm spectrum scale fundamentals workshop for americas part 7 spectrumscale el...xKinAnx This document provides guidance on sizing and configuring Spectrum Scale and Elastic Storage Server solutions. It discusses collecting information from clients such as use cases, workload characteristics, capacity and performance goals, and infrastructure requirements. It then describes using tools to help architect solutions that meet the client's needs, such as breaking the problem down, addressing redundancy and high availability, and accounting for different sites, tiers, clients and protocols. The document also provides tips for working with the configuration tool and pricing the solution appropriately.
Ibm spectrum scale fundamentals workshop for americas part 8 spectrumscale ba...
Ibm spectrum scale fundamentals workshop for americas part 8 spectrumscale ba...xKinAnx The document provides an overview of key concepts covered in a GPFS 4.1 system administration course, including backups using mmbackup, SOBAR integration, snapshots, quotas, clones, and extended attributes. The document includes examples of commands and procedures for administering these GPFS functions.
Ibm spectrum scale fundamentals workshop for americas part 5 ess gnr-usecases...
Ibm spectrum scale fundamentals workshop for americas part 5 ess gnr-usecases...xKinAnx This document provides an overview of Spectrum Scale 4.1 system administration. It describes the Elastic Storage Server options and components, Spectrum Scale native RAID (GNR), and tips for best practices. GNR implements sophisticated data placement and error correction algorithms using software RAID to provide high reliability and performance without additional hardware. It features auto-rebalancing, low rebuild overhead through declustering, and end-to-end data checksumming.
Presentation disaster recovery in virtualization and cloud
Presentation disaster recovery in virtualization and cloudxKinAnx The document discusses business continuity and disaster recovery in virtual and cloud environments, emphasizing that no single solution fits all situations as each implementation is unique. It outlines various disaster recovery strategies at both host and site levels, such as vMotion and VMware HA, and addresses considerations for stretched clusters and recovery plans. Additionally, it introduces vSphere replication and the circumstances under which to use site recovery manager for effective disaster recovery.
Presentation disaster recovery for oracle fusion middleware with the zfs st...
Presentation disaster recovery for oracle fusion middleware with the zfs st...xKinAnx The document discusses disaster recovery (DR) for Oracle Fusion Middleware (FMW) using the ZFS Storage Appliance, highlighting the increasing importance of minimizing downtime and data loss. It details how the ZFS Storage Appliance enhances DR capabilities, integrates seamlessly with Oracle Data Guard, and provides cost-effective, efficient management and redundancy for FMW environments. Best practices for deploying and managing DR with the ZFS Storage Appliance are also outlined, emphasizing the benefits of simplicity, reduced risk, and lower ownership costs.
Presentation differentiated virtualization for enterprise clouds, large and...
Presentation differentiated virtualization for enterprise clouds, large and...xKinAnx The document discusses IBM's Power Systems and their role in cloud computing, highlighting differentiated virtualization for enterprise workloads. It emphasizes the automation, scalability, and enhanced security capabilities that facilitate the deployment of private, public, and hybrid cloud solutions. Additionally, it outlines the advantages of automated service management, improved compliance, and cost efficiency provided by IBM's cloud offerings.
Presentation desktops for the cloud the view rollout
Presentation desktops for the cloud the view rolloutxKinAnx The document outlines VMware View, a centralized desktop solution that hosts operating systems in a virtual machine at a data center, facilitating remote access and offering advantages like reduced costs and enhanced security. It details implementation methodology, different types of virtual machines (linked clones and full VMs), and the architecture of clusters and hosts necessary for operation. Key benefits include streamlined management, automatic updates, and flexibility in resource allocation, making it suitable for diverse user needs.
Ad
Recently uploaded (20)
OpenPOWER Foundation & Open-Source Core Innovations
OpenPOWER Foundation & Open-Source Core InnovationsIBM penPOWER offers a fully open, royalty-free CPU architecture for custom chip design.
It enables both lightweight FPGA cores (like Microwatt) and high-performance processors (like POWER10).
Developers have full access to source code, specs, and tools for end-to-end chip creation.
It supports AI, HPC, cloud, and embedded workloads with proven performance.
Backed by a global community, it fosters innovation, education, and collaboration.
OWASP Barcelona 2025 Threat Model Library
OWASP Barcelona 2025 Threat Model LibraryPetraVukmirovic Threat Model Library Launch at OWASP Barcelona 2025
https://owasp.org/www-project-threat-model-library/
"Database isolation: how we deal with hundreds of direct connections to the d...
"Database isolation: how we deal with hundreds of direct connections to the d...Fwdays What can go wrong if you allow each service to access the database directly? In a startup, this seems like a quick and easy solution, but as the system scales, problems appear that no one could have guessed.
In my talk, I'll share Solidgate's experience in transforming its architecture: from the chaos of direct connections to a service-based data access model. I will talk about the transition stages, bottlenecks, and how isolation affected infrastructure support. I will honestly show what worked and what didn't. In short, we will analyze the controversy of this talk.
Using the SQLExecutor for Data Quality Management: aka One man's love for the...
Using the SQLExecutor for Data Quality Management: aka One man's love for the...Safe Software The SQLExecutor is one of FME’s most powerful and flexible transformers. Pivvot maintains a robust internal metadata hierarchy used to support ingestion and curation of thousands of external data sources that must be managed for quality before entering our platform. By using the SQLExecutor, Pivvot can efficiently detect problems and perform analysis before data is extracted from our staging environment, removing the need for rollbacks or cycles waisted on a failed job. This presentation will walk through three distinct examples of how Pivvot uses the SQLExecutor to engage its metadata hierarchy and integrate with its Data Quality Management workflows efficiently and within the source postgres database. Spatial Validation –Validating spatial prerequisites before entering a production environment. Reference Data Validation - Dynamically validate domain-ed columns across any table and multiple columns per table. Practical De-duplication - Removing identical or near-identical well point locations from two distinct source datasets in the same table.
Coordinated Disclosure for ML - What's Different and What's the Same.pdf
Coordinated Disclosure for ML - What's Different and What's the Same.pdfPriyanka Aash Coordinated Disclosure for ML - What's Different and What's the Same
Cracking the Code - Unveiling Synergies Between Open Source Security and AI.pdf
Cracking the Code - Unveiling Synergies Between Open Source Security and AI.pdfPriyanka Aash Cracking the Code - Unveiling Synergies Between Open Source Security and AI
" How to survive with 1 billion vectors and not sell a kidney: our low-cost c...
" How to survive with 1 billion vectors and not sell a kidney: our low-cost c...Fwdays Let's talk about our history. How we started the project with a small vector database of less than 2 million records. Later, we received a request for +100 million records, then another +100... And so gradually we reached almost 1 billion. Standard tools were quickly running out of steam - we were running into performance, index size, and very limited resources. After a long series of trials and errors, we built our own low-cost cluster, which today stably processes thousands of queries to more than 1B vectors.
Enhance GitHub Copilot using MCP - Enterprise version.pdf
Enhance GitHub Copilot using MCP - Enterprise version.pdfNilesh Gule Slide deck related to the GitHub Copilot Bootcamp in Melbourne on 17 June 2025
A Constitutional Quagmire - Ethical Minefields of AI, Cyber, and Privacy.pdf
A Constitutional Quagmire - Ethical Minefields of AI, Cyber, and Privacy.pdfPriyanka Aash A Constitutional Quagmire - Ethical Minefields of AI, Cyber, and Privacy
OpenACC and Open Hackathons Monthly Highlights June 2025
OpenACC and Open Hackathons Monthly Highlights June 2025OpenACC The OpenACC organization focuses on enhancing parallel computing skills and advancing interoperability in scientific applications through hackathons and training. The upcoming 2025 Open Accelerated Computing Summit (OACS) aims to explore the convergence of AI and HPC in scientific computing and foster knowledge sharing. This year's OACS welcomes talk submissions from a variety of topics, from Using Standard Language Parallelism to Computer Vision Applications. The document also highlights several open hackathons, a call to apply for NVIDIA Academic Grant Program and resources for optimizing scientific applications using OpenACC directives.
Securing Account Lifecycles in the Age of Deepfakes.pptx
Securing Account Lifecycles in the Age of Deepfakes.pptxFIDO Alliance Securing Account Lifecycles in the Age of Deepfakes
9-1-1 Addressing: End-to-End Automation Using FME
9-1-1 Addressing: End-to-End Automation Using FMESafe Software This session will cover a common use case for local and state/provincial governments who create and/or maintain their 9-1-1 addressing data, particularly address points and road centerlines. In this session, you'll learn how FME has helped Shelby County 9-1-1 (TN) automate the 9-1-1 addressing process; including automatically assigning attributes from disparate sources, on-the-fly QAQC of said data, and reporting. The FME logic that this presentation will cover includes: Table joins using attributes and geometry, Looping in custom transformers, Working with lists and Change detection.
Techniques for Automatic Device Identification and Network Assignment.pdf
Techniques for Automatic Device Identification and Network Assignment.pdfPriyanka Aash Techniques for Automatic Device Identification and Network Assignment
"Scaling in space and time with Temporal", Andriy Lupa.pdf
"Scaling in space and time with Temporal", Andriy Lupa.pdfFwdays Design patterns like Event Sourcing and Event Streaming have long become standards for building real-time analytics systems. However, when the system load becomes nonlinear with fast and often unpredictable spikes, it's crucial to respond quickly in order not to lose real-time operating itself.
In this talk, I’ll share my experience implementing and using a tool like Temporal.io. We'll explore the evolution of our system for maintaining real-time report generation and discuss how we use Temporal both for short-lived pipelines and long-running background tasks.
Security Tips for Enterprise Azure Solutions
Security Tips for Enterprise Azure SolutionsMichele Leroux Bustamante Delivering solutions to Azure may involve a variety of architecture patterns involving your applications, APIs data and associated Azure resources that comprise the solution. This session will use reference architectures to illustrate the security considerations to protect your Azure resources and data, how to achieve Zero Trust, and why it matters. Topics covered will include specific security recommendations for types Azure resources and related network security practices. The goal is to give you a breadth of understanding as to typical security requirements to meet compliance and security controls in an enterprise solution.
2025_06_18 - OpenMetadata Community Meeting.pdf
2025_06_18 - OpenMetadata Community Meeting.pdfOpenMetadata The community meetup was held Wednesday June 18, 2025 @ 9:00 AM PST.
Catch the next OpenMetadata Community Meetup @ https://www.meetup.com/openmetadata-meetup-group/
In this month's OpenMetadata Community Meetup, "Enforcing Quality & SLAs with OpenMetadata Data Contracts," we covered data contracts, why they matter, and how to implement them in OpenMetadata to increase the quality of your data assets!
Agenda Highlights:
👋 Introducing Data Contracts: An agreement between data producers and consumers
📝 Data Contracts key components: Understanding a contract and its purpose
🧑🎨 Writing your first contract: How to create your own contracts in OpenMetadata
🦾 An OpenMetadata MCP Server update!
➕ And More!
Quantum AI: Where Impossible Becomes Probable
Quantum AI: Where Impossible Becomes ProbableSaikat Basu Imagine combining the "brains" of Artificial Intelligence (AI) with the "super muscles" of Quantum Computing. That's Quantum AI!
It's a new field that uses the mind-bending rules of quantum physics to make AI even more powerful.
GenAI Opportunities and Challenges - Where 370 Enterprises Are Focusing Now.pdf
GenAI Opportunities and Challenges - Where 370 Enterprises Are Focusing Now.pdfPriyanka Aash GenAI Opportunities and Challenges - Where 370 Enterprises Are Focusing Now
Raman Bhaumik - Passionate Tech Enthusiast
Raman Bhaumik - Passionate Tech EnthusiastRaman Bhaumik A Junior Software Developer with a flair for innovation, Raman Bhaumik excels in delivering scalable web solutions. With three years of experience and a solid foundation in Java, Python, JavaScript, and SQL, she has streamlined task tracking by 20% and improved application stability.
Presentation database security audit vault & database firewall
- 1. Database Security Audit Vault & Database Firewall Morana Kobal Butković Senior Sales Consultant
- 2. Database Defense-in-Depth Access Control • Oracle Database Vault • Oracle Label Security • Oracle Advanced Security • Oracle Secure Backup • Oracle Data Masking Encryption and Masking Auditing and Monitoring • Oracle Audit Vault • Oracle Configuration Management • Oracle Total Recall • Oracle Database Firewall Blocking and Logging Encryption & Masking Access Control Auditing & Monitoring Blocking & Logging
- 3. <Insert Picture Here> Oracle Audit Vault
- 4. Oracle Audit Vault Business Drivers • Detective controls • Monitor privileged application user accounts for non-compliant activity – trust but verify • Audit non-application access to sensitive data (credit card, financial data, personal identifiable information, etc) • Verify that no one is trying to bypass the application security controls • PO line items are changed so it does not require more approvals • Cost of compliance • Eliminate costly and complex scripts for reporting • Reduce reporting costs for specific compliance audits • SOX, PCI, HIPAA, SAS 70, STIG
- 5. Oracle Audit Vault Automated Activity Monitoring & Audit Reporting • Consolidate audit data into secure repository • Detect and alert on suspicious activities • Out-of-the box compliance reporting • Centralized audit policy management CRM Data ERP Data Databases HR Data Audit Data Policies Built-in Reports Alerts Custom Reports ! Auditor
- 6. Oracle Audit Vault Oracle Database Audit Support • Database Audit Tables • Collect audit data for standard and fine-grained auditing • Oracle audit trail from OS files • Collect audit records written in XML or standard text file • Operating system SYSLOG • Collect Oracle database audit records from SYSLOG • Redo log • Extract before/after values and DDL changes to table • Database Vault specific audit records User Object Statement Privilege Condition AUD$ REDO Log FGA_LOG$ Audit on Logged in OS Logs
- 7. Applying Fine-Grained Auditing DBMS_FGA.ADD_POLICY ( object_schema => ‘OE', object_name => ‘ORDERS', policy_name => ‘NONAPPSUSER, audit_condition => SYS_CONTEXT('USERENV','SESSION_USER')<> 'APPS' , enable => TRUE, statement_types => 'SELECT' ); Generate Audit Record Enforce Audit Policy in Database ... SYS_CONTEXT('USERENV','SESSION_USER')<>'APPS' Select names, salary from ORDERS where...
- 8. Oracle Audit Vault Heterogeneous Database Support • Microsoft SQL server versions 2000, 2005, & 2008 • Server side trace – set specific audit event • Windows event audit – specific audit events that are viewed by the windows event viewer • C2 - automatically sets all auditable events and collects them in the audit log • Support for 2008 audit facility targeted for CY2010 • IBM DB2 8.2 - 9.5 on Linux, Unix, Windows • Extract binary audit files into a trace file • Sybase ASE 12.5.4 - 15.0.x • Utilize the native audit tables
- 9. Secure & Scalable Audit Warehouse • Audit Warehouse • Document Schema • Enable BI and analysis • Performance and Scalability • Built-in partitioning • Database compression • Scales to Terabytes • Certified with Oracle RAC • Protected with Built-in Security • Encrypted audit data transmission • Separation of Duty provided by Database Vault • Audit Vault Administrator • Audit Vault Auditor
- 10. Audit Vault User Entitlements • View all user accounts in the Oracle database • Retrieve a snapshot of user entitlement data • Filter data based on users or privileges • View or print report in PDF format • Compare changes in user accounts and privileges • View SYSDBA/SYSOPER privileges
- 11. Database User Privileges Report • Display all Oracle database users, privileges, and roles • Reports accounts and their level of access • Regulations: SOX, PCI, HIPAA, SAS 70, STIG
- 12. User Account Details Account, Roles, System/Object Privileges
- 14. Reports Management Schedule, Retention, Notification, Attestation
- 15. Oracle Audit Vault Alerts Threat Detection with Custom Alerts • Alerts can be defined for • Creating users on sensitive systems • Role grants on sensitive systems • “DBA” grants on all systems • Failed logins for application users • Directly viewing sensitive columns • …. • Add workflow for alerts • Track alerts • Drill down from the dashboard • Send alerts to distribution lists
- 16. Integration with Email / SMS / Remedy FRM: Audit Vault SUBJ: Audit Vault Alert : Create User MSG: Create User occurred On PAYROLL.ORACLE.COM @ 02-Oct-09 11:07:10 AM
- 17. Oracle Recommended Audit Settings • Auditing should be selective and effective – target privileges users, selective tables, and secure configurations • Oracle Database 11g provides default audit policy configuration ALTER ANY PROCEDURE CREATE ANY JOB DROP ANY TABLE ALTER ANY TABLE CREATE ANY LIBRARY DROP PROFILE ALTER DATABASE CREATE ANY PROCEDURE DROP USER ALTER PROFILE CREATE ANY TABLE EXEMPT ACCESS POLICY AUDIT ROLE BY ACCESS CREATE EXTERNAL JOB GRANT ANY OBJECT PRIVILEGE ALTER SYSTEM CREATE PUBLIC DATABASE LINK GRANT ANY PRIVILEGE ALTER USER CREATE SESSION GRANT ANY ROLE AUDIT SYSTEM CREATE USER AUDIT SYSTEM BY ACCESS DROP ANY PROCEDURE Included in the demo directory of the Audit Vault Server: $ORACLE_HOME/demo/secconf.sql
- 18. Auditing Resources Impact on CPU performance • Original workload CPU 1.08% for 10 audit/sec case • Original workload CPU 1.56% for 100 audit/sec case Database auditing / No Audit Vault Audit Vault collection turned on Database auditing / No Audit Vault Audit Vault collection turned on Audit Load 10 records / second 10 records / second 100 records / second 100 records / second OS Log 0.08% 0.7% 0.15% 2.7% DB Audit 0.13% 0.5% 1.6% 3.4% Redo 0% 3.7% 0% 8.2% Audit Source *Internal testing: Source: 4x32GB 3GHz Intel Xeons RHEL3.0, running 2 Oracle Database 10.2.0.3.0 AV Server: 2x6GB 3GHz Intel Xeons RHEL3.0, AV Server 10.2.2.0.0
- 19. <Insert Picture Here> New Product: Oracle Database Firewall
- 20. Oracle Database Firewall First Line of Defense • Monitor database activity on network and log/block unauthorized database access • Highly accurate SQL grammar based analysis to enforce normal activity • Built-in and custom compliance reports for SOX, PCI, and other regulations
- 21. Challenges of a Database Firewall • Building accurate policy profiles of good application behavior with changes over time • Performance to your application as the number of transactions increase over the network • Needing to throw more hardware on the network to handle my workload for scalability
- 22. Security Model and Policy Enforcement • Policy Enforcement • Performance and scalability since millions of statements can be simplified into a small number of SQL characteristics or “clusters” • High level of accuracy • Flexible enforcement: block, substitute, alert and pass, log only • Policies are easily configured using: • White List • Can be automatically generated for any application • “Allowed” behavior can be defined for any user or application • Transactions found not to match the policy instantly rejected • Black List • Stop unwanted transactions, users or schema access • Prevent privilege or role escalation and illegal access to sensitive data by using factors • Selectively block any part of transaction in context to your business and security goals
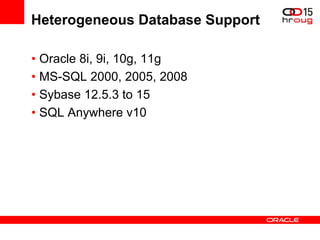
- 23. Heterogeneous Database Support • Oracle 8i, 9i, 10g, 11g • MS-SQL 2000, 2005, 2008 • Sybase 12.5.3 to 15 • SQL Anywhere v10
- 24. The Basic Components • Creates security policies • Runs on Windows desktop • Reports, archives repository • Firewall mgmt, policy mgmt • Alerts, integration • Reads SQL traffic on the network • Logs/Blocks unauthorized traffic • Monitors access Database Firewall Database Firewall Management Server Policy Analyzer Database Firewall (HA Mode) Remote/Local Monitor • Capture network traffic on DB host and forwards it to DBFW • Capture non-network traffic on DB host and sends it to the DBFW
- 25. Oracle Database Firewall Flexible Deployment Model • Deploy on customer’s existing or new hardware: • Runs Oracle Enterprise Linux base operating system • Firewall blocking mode requires certified NIC card • Scales vertically • Add CPU, disk, and memory to the servers versus adding more and more appliances • Database Firewall and Database Firewall Management Server can co-reside
- 26. Oracle Database Firewall Out of Band Deployment Mode • Monitor Only Mode – No Blocking • Also known as “SPAN” or “Span port” or “Mirrored” or “Tap” • SQL logging and reporting only • Easy for demo / POC or lab test • Easy to deploy, no risk of impacting databases or applications
- 27. Oracle Database Firewall In-Line Deployment Modes • Blocking and Monitoring • SQL traffic is inspected and verified against policy • Also known as a “Bridge” or “transparent bridge” • Sometimes only option if out-of-band ports are not available
- 28. Reporting • Database Firewall log data consolidated into reporting database • Over 130 built in reports that can be modified/customized • Entitlement report for database attestation • Activity and privileged user reports • Supports demonstrating PCI, SOX, HIPAA, etc.
- 29. Accurate, Scalable, Flexible • Most accurate Zero false positives and the competition can never get the policy created • Most scalable Scales easily by adding more CPU’s, more disk, more memory to accommodate growth. • Most flexible Software and can be deployed onto any server that supports OEL. These platforms can be servers, blades or virtual platforms.
- 30. Fast, Transparent, Open • Fastest You get more transactions through put per second that an equivalent competitive solution • Easiest to deploy Ability to understand the SQL language and categorize 10’s of thousands of transactions, results in simple policy configuration • Open Reporting Documented database tables enables customers to use virtually any reporting tool to extract forensic or summary data.